You’ve seen that little message a thousand times, “Messages are end-to-end encrypted.” WhatsApp shows it. The Signal shows it. Even your bank app says something similar.
But what does it actually mean? And more importantly, does it actually protect you?
In 2026, that second question matters more than ever. Because the answer is: it depends on more than just encryption.
Let’s break the whole thing down; plainly, honestly, with no jargon left unexplained.
The Problem That Encryption Is Solving
Imagine you write a letter, seal it, and post it. But every post office it passes through can open it, read it, reseal it, and send it on. You’d never know.
That’s exactly how unencrypted messages work online. Your message travels through servers, your internet provider’s, the app company’s, sometimes government infrastructure, and anyone with access can read it.
End-to-end encryption (E2EE) seals that envelope so tightly that nobody in the middle can open it. Not the app company. Not your ISP. Not a hacker sitting on the same Wi-Fi as you. Only you and the person you’re talking to hold the key.
That’s the promise. Now let’s see how it actually works, and where it gets complicated.
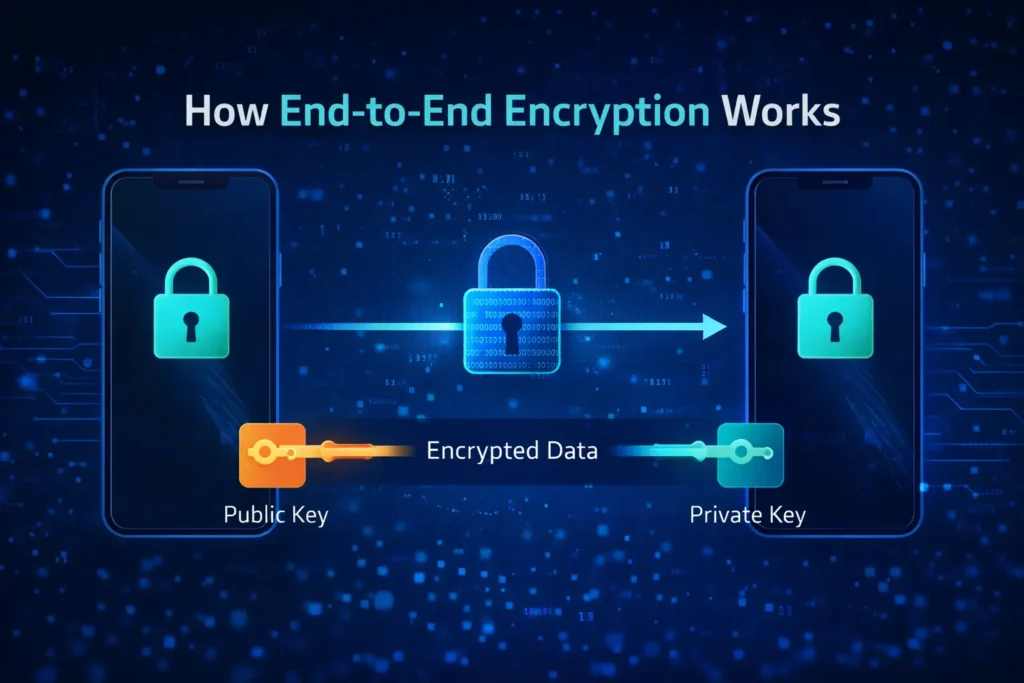
The Lock and Key System (Public & Private Keys)
This is the core idea. Once you understand this, everything else makes sense.
When you use an E2EE app, your device automatically generates two mathematically linked keys:
- Public Key: Your lock. Shared openly with everyone. Anyone can use it to encrypt (lock) a message meant for you.
- Private Key: The only thing that can decrypt (unlock) those messages. It never leaves your device. Ever.
Here’s what happens when your friend sends you a message:
- Their app fetches your public key from the server
- It uses that to scramble the message into unreadable gibberish
- The encrypted message travels through the app’s servers
- Only your private key sitting on your phone can unscramble it
The server in the middle only ever sees a locked box. It has no key. It cannot open it.
This system is called asymmetric encryption, and it’s the backbone of modern digital privacy.
What Encrypted Data Actually Looks Like
You send: “Meet me at 6 pm.”
What travels through the server looks like this:
aJ93kLpQ8mVx2Tr+nBz7HqWsYd1/Kc0FiRoEuN4gXb==
That’s not an exaggeration. Encrypted data is genuinely meaningless to anyone without the private key, even if they intercept it perfectly. They get noise.
How WhatsApp Does It – The Signal Protocol
WhatsApp (and Signal, and now Messenger) uses something called the Signal Protocol, widely considered the gold standard of messaging encryption.
What makes it especially clever: it doesn’t use just one key for your entire conversation. It generates a brand new encryption key for every single message.
So even if someone somehow cracked one message, they can’t use that crack to read anything before or after it. Each message is independently locked. This is called Forward Secrecy, and it’s a significant security feature.
The Backup Loophole – The Biggest Privacy Risk Most People Miss
Here’s where the honest conversation gets uncomfortable.
The encryption described above is real. It works. Independent cryptographers confirm it. But it only protects your message while it’s travelling between phones.
The moment that message lands on your device and gets backed up to Google Drive or iCloud, it steps outside the encrypted world entirely.
WhatsApp does offer an encrypted backup option. But it is off by default. You have to manually go into settings, enable it, and create either a strong password or a 64-digit encryption key. Most users never do this. Most users don’t even know the option exists.
And here’s the part that makes it worse: even if you turn on encrypted backups, the people you chat with probably haven’t. That means their copy of your conversation, the same messages, sits in an unencrypted cloud backup. Your half is locked. Their half isn’t.
This is what Telegram’s founder, Pavel Durov, called out publicly in April 2026, claiming roughly 95% of WhatsApp messages ultimately end up as plain-text backups on Apple or Google servers. WhatsApp responded, calling the claims “categorically false and absurd,” and independent cryptographers largely agree that the core encryption itself is solid. But the backup architecture vulnerability? That part is well-documented and real; the Electronic Frontier Foundation (EFF) has warned about it for years.
The bottom line: the lock is genuinely strong. The loophole is also genuinely real.
What you should do right now: WhatsApp → Settings → Chats → Chat Backup → End-to-End Encrypted Backup → Turn it on. It takes 30 seconds.
The Metadata Problem: They Don’t Know What You Said, But They Know Everything Else
Even when encryption is working perfectly, there’s a layer that apps still see: metadata.
Metadata isn’t what you said. It’s everything around what you said:
- Who did you talk to
- When you talked to them
- How often
- How long did the conversation last
- Your IP address (which reveals approximate location)
WhatsApp, as a Meta product, collects significant metadata. In a legal investigation, authorities may not be able to read your messages, but seeing that you called a specific person repeatedly at 2 AM is often enough to build a case without ever reading a word.
Signal is the clear outlier here. It’s architecturally designed to know almost nothing about you, not even your contact list. That’s why privacy researchers consistently recommend it over every other option.
Encryption hides what you said. Metadata reveals the pattern of your life.
Which Apps Actually Use E2EE? (2026 Updated)
Not all apps are equal, and the details matter more than the headline claim:
| App | E2E Encrypted? | Backups Encrypted by Default? | Metadata Collected? |
|---|---|---|---|
| ✅ Yes | ❌ No (opt-in only) | ⚠️ Yes (Meta) | |
| Signal | ✅ Yes | ✅ Yes | ❌ Minimal by design |
| iMessage | ✅ Apple to Apple | ⚠️ iCloud backup risk | ⚠️ Some |
| Telegram | ⚠️ Secret Chats only | ❌ No | ⚠️ Yes |
| Facebook Messenger | ✅ Yes (default since 2024) | ❌ No | ⚠️ Yes (Meta) |
| Regular SMS | ❌ No | ❌ No | ❌ Fully exposed |
| Gmail | ❌ No (by default) | ❌ No | ⚠️ Yes (Google) |
Note on Telegram: It’s a common misconception that Telegram is fully encrypted. Standard Telegram chats use client-server encryption, meaning Telegram’s own servers can technically read them. Only “Secret Chats” use true E2EE. Ironically, this makes Durov’s WhatsApp criticism somewhat selective.
Is End-to-End Encryption Actually Unbreakable?
The encryption mathematics, usually AES-256, would take a standard computer billions of years to crack by brute force. So yes, the math is essentially unbreakable with current technology.
But “unbreakable encryption” doesn’t mean “total privacy.” The weakest points are never the encryption itself; they’re everything around it:
- Unencrypted cloud backups – the #1 real-world vulnerability in 2026
- Your unlocked physical phone – if someone picks it up, they read everything
- The other person’s device – screenshots exist, and encryption can’t stop them
- Malware or spyware – reads your messages before they’re encrypted at the source
- Metadata – your communication patterns, even without message content
The encryption is the strongest part of the chain. Focus your attention on the weakest links.
Why Governments Want a Backdoor (And Why That’s Dangerous)
Law enforcement agencies worldwide have repeatedly pushed for a “backdoor”, a secret access route built into E2EE so they can read messages during investigations.
Security experts oppose this unanimously, for one clear reason: a backdoor that only good guys can use does not exist. The moment a backdoor is built, it becomes a vulnerability. If a government can use it, so can hackers who find it. You cannot build a door that only opens for the right people.
Companies like Apple and Signal have refused to comply. The debate continues, with no easy resolution in sight.
The Simple Version Start to Finish
If you want to explain E2EE to someone in two minutes:
- Your message gets scrambled by a unique lock before it leaves your phone
- It travels as unreadable gibberish through the internet
- Only the recipient’s device holds the matching key
- Nobody in the middle can read it, including the app company
- But if it gets backed up to the cloud without encrypted backup enabled, that protection ends there
That last point is what most people and most articles leave out.
❓ FAQ: End-to-End Encryption
Q1: Does end-to-end encryption mean WhatsApp can’t read my messages?
Technically, yes – WhatsApp’s servers only receive encrypted data and hold no decryption keys. However, if messages are backed up to Google Drive or iCloud without an encrypted backup enabled, those copies may be accessible to Apple, Google, or governments through legal requests.
Q2: Is Signal safer than WhatsApp?
Both use the identical Signal Protocol for message encryption. Signal is considered more privacy-focused overall because it collects minimal metadata, stores almost nothing about users, and its entire codebase is open-source and publicly audited.
Q3: Are WhatsApp backups encrypted?
Not by default. You must manually enable End-to-End Encrypted Backup in WhatsApp Settings → Chats → Chat Backup. Without this, your Google Drive or iCloud backup is not protected by E2EE and can potentially be accessed by third parties or through government legal requests.
Q4: Is WhatsApp’s encryption actually fraud, like Durov claimed?
The core encryption technology is technically solid and verified by independent cryptographers. The real and legitimate concern is about unencrypted cloud backups, not the encryption itself. It’s worth noting that Durov runs Telegram, WhatsApp’s direct competitor, and Telegram’s own standard chats are not end-to-end encrypted by default either.
Q5: Can the government access my WhatsApp messages?
Not the encrypted message content directly. However, they can legally request metadata (who you talked to, when) from WhatsApp, and may also request unencrypted backup data from Apple or Google if you haven’t enabled encrypted backups.
Q6: What is the difference between encryption and end-to-end encryption?
Standard encryption protects data from outsiders, but the service provider still holds a decryption key, meaning they can read your data if required. E2EE means only the sender and receiver hold keys. Not even the service provider can decrypt it.
Q7: Is end-to-end encryption only for messages?
No. E2EE is also used for video calls (WhatsApp, FaceTime, Signal), file transfers, emails (ProtonMail), and cloud storage (Tresorit, iCloud with Advanced Data Protection enabled).
Q8: What is the most private messaging app in 2026?
Signal, consistently. It uses E2EE by default, encrypts backups, collects minimal metadata, and is fully open-source – meaning its security can be independently verified by anyone.